Communication protocols are the invisible foundation of our connected world. From the moment you opened this webpage to the real-time notifications on your smartphone, countless protocols worked in harmony to deliver information seamlessly across networks. Understanding these protocols isn't just academic—it's essential for building robust, scalable systems in today's interconnected landscape.
What Are Communication Protocols?
Communication protocols are formalized rule sets for data exchange between systems. They tell devices how to discover each other, establish connections, exchange information, handle errors, and terminate sessions. Without them, network communication would collapse into chaos.
Think of protocols as diplomatic treaties between systems. Just as countries need agreements on trade procedures, data exchange requires standardized methods for several concerns. Format defines how data should be structured, while timing governs when to send and receive it. Error handling determines what happens when things go wrong. Authentication covers verifying identity and permissions, and flow control manages data transmission rates to prevent overwhelming receivers.
Historical Evolution: From ARPANET to Internet
The story of communication protocols is inseparable from the evolution of the Internet itself.
The ARPANET Era (1960s-1970s)
The Advanced Research Projects Agency Network (ARPANET) introduced the first packet-switching network protocols. The Network Control Protocol (NCP) was the original standard, but it had significant limitations. NCP supported host-to-host communication only, with no ability to route between networks. It offered no error recovery mechanisms, and its limited scalability made it unsuitable for the growing internetwork that researchers envisioned.
The TCP/IP Revolution (1970s-1980s)
Vint Cerf and Bob Kahn revolutionized networking with the Internet Protocol Suite:
This separation of concerns—with IP handling routing and TCP managing reliable delivery—became the foundation of modern networking.
The World Wide Web (1990s)
Tim Berners-Lee's invention of HTTP transformed the Internet from a research tool into a global information system:
- 1991: First web server and browser
- 1993: HTTP/1.0 specification
- 1999: HTTP/1.1 with persistent connections
- 2015: HTTP/2 with multiplexing and compression
The OSI Model: A Layered Approach
The Open Systems Interconnection (OSI) model provides a conceptual framework for understanding network protocols. It is a map, not a protocol suite. Each layer has specific responsibilities and communicates with adjacent layers.
OSI Model layers showing the hierarchical structure of network communication. Data flows down through layers (encapsulation) on the sender side and up through layers (de-encapsulation) on the receiver side. Each layer provides services to the layer above it.
Layer 7: Application Layer
Purpose: Provides network services directly to applications Key Protocols: HTTP/HTTPS, FTP, SMTP, DNS, DHCP
The application layer is where users interact with network services. Modern web applications heavily rely on:
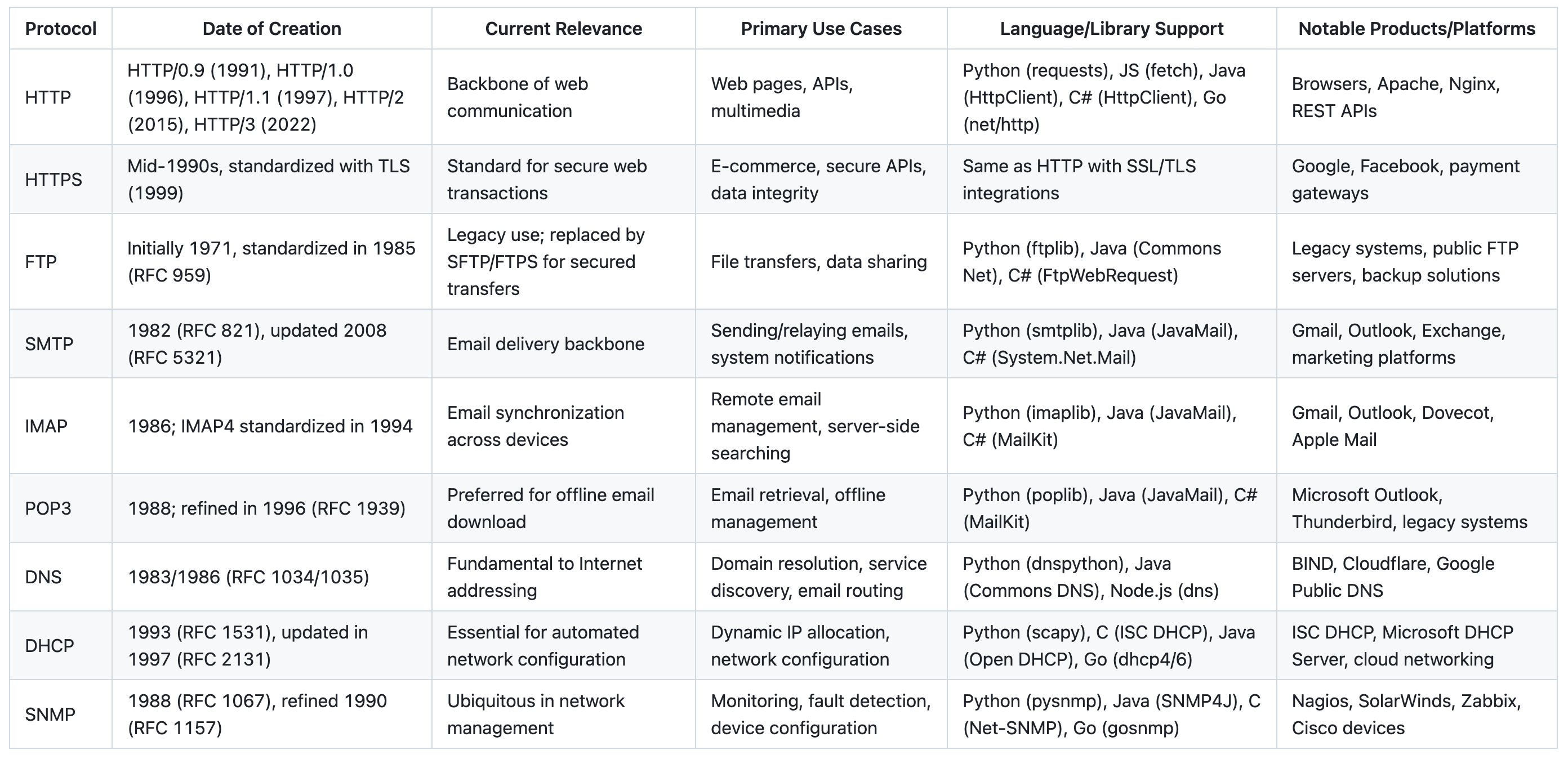
HTTP/HTTPS: The Web's Foundation
HTTP (Hypertext Transfer Protocol) is the cornerstone of web communication. The protocol is stateless, meaning each request is independent of every other. It follows a request-response model where the client initiates and the server responds. HTTP defines several methods (GET, POST, PUT, DELETE, PATCH, etc.) for different operations, and servers reply with status codes like 200 (OK), 404 (Not Found), and 500 (Server Error) to indicate the outcome.
HTTPS adds TLS/SSL encryption on top of HTTP. It gives you three guarantees. Confidentiality keeps data unreadable in transit, Integrity confirms it was not tampered with during transmission, and Authentication verifies the server's identity through certificates.
FTP: File Transfer Protocol
Still widely used for bulk file transfers:
DNS: The Internet's Phone Book
Domain Name System translates human-readable domain names to IP addresses:
Layer 4: Transport Layer
Purpose: Provides reliable data transfer between applications Key Protocols: TCP, UDP, QUIC
TCP (Transmission Control Protocol)
TCP is connection-oriented, meaning it establishes a session before any data transfer begins. It is reliable: every packet is acknowledged, and the protocol guarantees both delivery and ordering. Built-in flow control manages transmission rates so a fast sender cannot overwhelm a slow receiver, and error recovery automatically retransmits lost packets.
Three-Way Handshake:
TCP three-way handshake establishing a reliable connection between client and server. The SYN-SYN/ACK-ACK sequence ensures both parties are ready for data transfer. Sequence numbers track packets, and acknowledgments confirm receipt, providing reliability.
UDP (User Datagram Protocol)
UDP takes the opposite approach to TCP. It is connectionless, requiring no session establishment before sending data. The protocol is deliberately unreliable — it offers no delivery guarantees and no ordering. This low overhead design keeps protocol headers minimal, making UDP fast and ideal for real-time applications.
That speed advantage explains UDP's typical use cases. DNS queries benefit from quick, stateless lookups where retrying a failed request is cheaper than maintaining a connection. Video streaming prioritizes speed over perfect delivery — a dropped frame matters less than a stalled playback. Online gaming demands real-time, low-latency communication where stale data is worse than missing data.
QUIC: The Next Generation
Quick UDP Internet Connections combines the best of TCP and UDP:
Layer 3: Network Layer
Purpose: Routes data between different networks Key Protocols: IP, ICMP, ARP
IP (Internet Protocol)
The Internet's addressing system:
IPv4 uses 32-bit addresses (e.g., 192.168.1.1). That gives us roughly ~4.3 billion unique addresses. The pool is effectively exhausted, which is why IPv6 adoption keeps rising.
IPv6 expands the address space dramatically with 128-bit addresses (e.g., 2001:db8::1), yielding 340 undecillion unique addresses — more than enough for every device on Earth many times over. IPv6 also introduces built-in security through mandatory IPsec support and native autoconfiguration, simplifying network setup.
ICMP (Internet Control Message Protocol)
Network diagnostic and error reporting:
Layer 2: Data Link Layer
Purpose: Manages access to physical network medium Key Protocols: Ethernet, Wi-Fi (802.11)
Ethernet
The dominant wired networking standard, Ethernet relies on CSMA/CD (Carrier Sense Multiple Access with Collision Detection) to arbitrate access to the shared medium. Devices are identified by MAC addresses — unique hardware-level identifiers burned into each network interface. Data is wrapped in a frame structure that handles encapsulation for network transmission.
Wi-Fi (802.11)
Wireless networking protocols:
- 802.11n: Up to 600 Mbps, 2.4/5 GHz
- 802.11ac: Up to 6.9 Gbps, 5 GHz
- 802.11ax (Wi-Fi 6): Up to 9.6 Gbps, improved efficiency
Protocol Families and Specializations
Real-Time Communication Protocols
WebRTC
Web Real-Time Communication enables peer-to-peer audio, video, and data sharing:
MQTT (Message Queuing Telemetry Transport)
Lightweight messaging protocol for IoT devices:
Security-Focused Protocols
TLS/SSL
Transport Layer Security provides encryption for various protocols:
SSH (Secure Shell)
Encrypted remote access protocol:
Modern Protocol Considerations
HTTP/3 and the QUIC Revolution
HTTP/3 builds on QUIC to address HTTP/2 limitations:
HTTP/2 introduced multiplexing. It still runs over a single TCP connection, and that creates problems. Head-of-line blocking means one lost packet stalls every multiplexed stream, TCP overhead still requires multiple round trips before application data can flow, and the congestion model remains too generic for diverse network conditions.
HTTP/3 addresses each of these shortcomings. Because QUIC gives each request its own independent stream, packet loss affects only that single stream while others continue uninterrupted. 0-RTT connections allow clients to resume previous sessions instantly, eliminating the handshake latency that plagues new TCP connections. Mobile users benefit most from better mobile performance, since QUIC handles network switching gracefully — moving from Wi-Fi to cellular no longer resets the connection.
GraphQL Over HTTP
GraphQL changes how we think about API protocols:
GraphQL offers several advantages over traditional REST. A single endpoint replaces the need for multiple API calls to different URLs. Precise data fetching lets clients request exactly the fields they need — no more over-fetching or under-fetching. The schema provides strong typing that drives development and enables powerful tooling. And built-in real-time subscriptions deliver live data updates without polling.
Protocol Buffers (Protobuf)
Efficient binary serialization for microservices:
Protobuf's advantages stem from its binary nature. Payloads are compact, significantly smaller than equivalent JSON. Serialization and deserialization are fast, reducing CPU overhead on both ends. The format is language agnostic — the protobuf compiler generates idiomatic code for multiple languages from a single .proto definition. And built-in schema evolution ensures backward and forward compatibility, so services can be upgraded independently without breaking communication.
Implementation Considerations
Choosing the Right Protocol Stack
For Web Applications:
For Microservices:
For IoT Systems:
Performance Optimization Strategies
Connection Pooling
Compression and Caching
Error Handling and Resilience
Circuit Breaker Pattern
Retry with Exponential Backoff
Future of Communication Protocols
Emerging Trends
Protocol Evolution Timeline:
Quantum-Resistant Security
Post-quantum cryptography will reshape protocol security:
Edge Computing Protocols
New protocols optimized for edge scenarios are emerging along three axes. Ultra-low latency designs target sub-millisecond communication for time-critical workloads. Mobile-first architectures handle frequent network changes as devices roam between towers and access points. And resource-constrained protocols minimize overhead so that IoT devices with limited CPU and memory can participate efficiently.
AI-Driven Protocol Selection
Machine learning will optimize protocol choice:
Best Practices for Modern Applications
API Design Principles
- RESTful Design with GraphQL Enhancement
- Versioning Strategy
- Rate Limiting and Throttling
Security Implementation
HTTPS Everywhere
API Security Headers
Monitoring and Observability
Protocol-Level Metrics
Distributed Tracing
Conclusion
Communication protocols form the invisible backbone of our digital world. They are everywhere. From simple web browsing to complex distributed systems, understanding the stack—from TCP/IP fundamentals to HTTP/3 and QUIC—is essential when you need robust, scalable applications.
Several themes run through the entire protocol landscape. Layered architecture, as embodied by the OSI model, provides a framework for understanding protocol responsibilities and isolating concerns. Protocol evolution is constant — standards continuously adapt to address new requirements and challenges. Every protocol involves trade-offs between reliability, performance, and complexity, and the right choice depends on your specific constraints. Modern protocols must adopt a security first posture, building encryption and authentication in from the ground up rather than bolting them on later. Finally, being future-ready means preparing for quantum-resistant cryptography and AI-optimized networking before they become urgent necessities.
As we move toward a more connected future with IoT, edge computing, and real-time applications, protocol choice matters even more. The concrete technologies will keep evolving. The underlying concerns of reliability, security, and performance will not.
Whether you're designing microservices, building real-time applications, or architecting IoT systems, remember that protocol selection is not just a technical decision—it's a strategic choice that impacts user experience, system reliability, and long-term maintainability.
Further Reading
Foundational Papers
- Cerf, V. & Kahn, R.E. (1974). "A Protocol for Packet Network Intercommunication" — IEEE Transactions on Communications 22(5). The foundational TCP/IP paper
- Fielding, R. (2000). "Architectural Styles and the Design of Network-Based Software Architectures" — PhD Dissertation, UC Irvine. The REST architectural style origin
IETF RFCs
- RFC 793: Transmission Control Protocol (TCP)
- RFC 791: Internet Protocol (IP)
- RFC 9110: HTTP Semantics — The modern HTTP/1.1 specification
- RFC 9113: HTTP/2
- RFC 9114: HTTP/3
- RFC 9000: QUIC — The transport protocol underlying HTTP/3
- RFC 6455: The WebSocket Protocol
Additional Resources
- Stenberg, D. "HTTP/2 Explained" — Accessible guide to HTTP/2 by the creator of curl
- gRPC Documentation — Official documentation for the gRPC framework
The world of communication protocols is vast and continuously evolving. Stay curious, keep learning, and remember that today's cutting-edge protocol is tomorrow's legacy system. Build with standards, but prepare for change.